This post we look deeper into the poorly understood world called the Deep Web. We’ll take a look at how large this hidden realm might be and the types of activities that take place far below the surface world of Google and Facebook.
Oddly enough, we seem to be surrounded by references to the deep web. Popular TV programs make quick references to this world as though everyone has a ready point of reference to what is down under the surface of Google searches and social media campaigns. The reality is,no one really knows just how big the deep web is. What we do know is that it hides the collaborative efforts of criminal gangs. The ever increasing onslaught against businesses and financial institutions comes from the deep web. Like the mythical monsters of a bygone era at sea, the dark forces that seek to steal millions strike from the unknown.
In the late 1960s, a handful of American universities linked their information networks on a time sharing model that we now know as the forerunner to the Internet. The US Department of Defense provided much of the funding and infrastructure to these universities as the concept grew. Various files and documents were shared, but there was no real index to find these items if the users were not talking and collaborating with each other. When they were shared, they were often sent over phone lines. Early pranksters and people who learned how to trick the phone systems became the first generation of hackers.
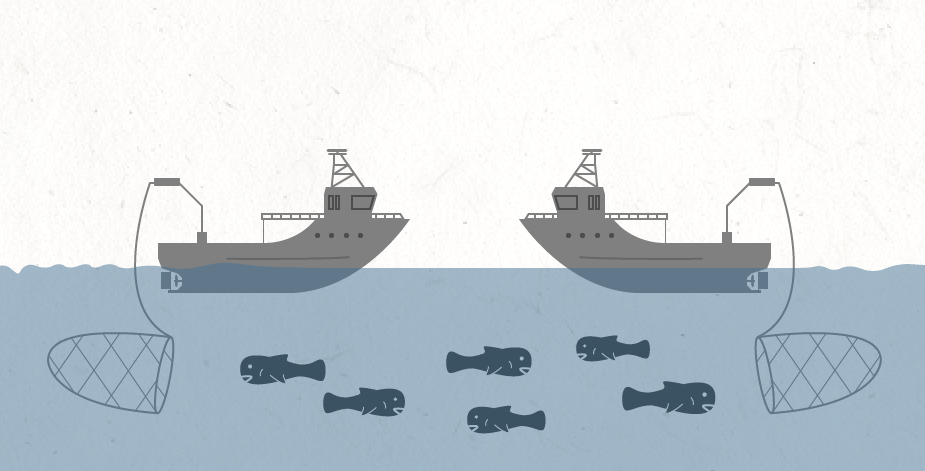
CNN Money has an infographic that gives a somewhat simplified overview of the Deep Web. There are roughly 500 million sites on the Internet that are accessed through what is known as the surface web. Estimates vary, but credible sources guess the Deep Web to be 500 times the size of the surface web. This causes the Deep Web to take on the qualities of legend, because it becomes difficult to conceptualize what is there,and what is going on. Law enforcement professionals find increasing amounts of time spent trying to investigate this murky world of hidden behavior.
SOURCE: CNN Money, Bitshare
As mentioned earlier, the origins of the Internet grew out of university and Government collaborations. The spirit of sharing information created an atmosphere where files were readily made available to colleagues. Networks were originally built and then linked together in increasingly complex systems. These formed the foundations for what we now refer to as the Deep Web. Networks were linked, but not always able to be indexed. Certain browsers like Mosaic could only read text files. As research money shifted and Government backed groups like the National Science Foundation ended support for networks infrastructure, the Deep Web continued to grow. Networks not regulated by Government policies became the larger part of the World Wide Web.
The culture of sharing and collaborating continued, but outside the campuses of universities and Government R&D facilities. Unscrupulous behavior began to creep in as intellectual property rights issues were ignored on a worldwide scale. Software piracy grew from a handful of poor kids sharing programs to economies of scale hidden under the surface web, communicating across bulletin board systems. Fraudulent activity became more prevalent as more and more regions of the globe came online. The number of potential victims seemed limitless, and the opportunities were now available every day, around the clock.
By 2002, the US Federal Bureau of Investigation formed a special Cyber Crimes unit with the purpose of investigating network intrusions, identity theft, and online fraud. Increasingly, cyber terrorism and espionage are becoming a focus of this unit. The efforts of this organization are not intended to limit the use of the Deep Web, only to try to pursue criminal activity that occurs there. Much like conventional crime fighting efforts, activities perpetrated by international criminal gangs can be much harder to pursue by national policing organizations. States that do not have strong investigative bodies, or that have unofficial lax policies toward cyber criminals, can offer a haven for massive attacks against targeted businesses and banking institutions.
SOURCE: Federal Bureau of Investigation, US Department of Justice
Anonymity became the prerequisite goal of people looking to pursue a life of less than honest means online. This was a unique challenge, because information systems have always tried to document everything from file updates to servers and IP addresses used. Savvy computer users taught the hackers the techniques to become anonymous online. So-called “Dark Web” networks formed with often poorly understood participants trying to conduct their business without being tracked.
TOR, an anonymous, private online network increasingly gained the attention of folks thanks to it’s “onion routing” technology supported by the US Navy (Office of Naval Research). This technology allowed for linking anonymous networks in the late 1990s with enduring technical hurdles being the focus of private and military R&D teams. DARPA, the folks behind the original network that became the Internet, joined the funding effort to foster further development of a viable network. By 2003, the TOR network was officially deployed with the codebase released under the (free) open MIT license.
SOURCE: Center for High Assurance Computer Systems, Information Security Buzz
RELATED: The Secret History of TOR
As the Deep Web grew and changed, real world events occurred that had ripple effects on the virtual world. An ongoing set of wars in the Middle East and Asia helped to drive black market operations that relied on the strength of anonymous support networks. Not only were drugs being traded in the Deep Web, but more sinister markets were developing for human traffickers, identity theft dossiers, and stolen antiquities. Criminal gangs became increasingly tech savvy and began building teams of hackers to launch attacks against targeted victims and then trade the stolen goods in their black markets. Trading values relied largely on the global reserve currency of the US dollar or the Euro, but the financial crisis of 2008 seems to have helped set the stage for an alternative: the Bitcoin.
ABOUT THE AUTHOR
Christoper Watson is an Information Technology professional with success in both public and private sector businesses. Technical and business experience is complimented with operational and strategic planning, international contracting work, leadership development and team building competency in challenging physical and political environments. Experience leverages strengths with technology services and providing timely and relevant information to senior executive leadership. Christopher is based out of the Oklahoma City office.





[…] RELATED: What is the Deep Web? […]