How to Allow Legit Network Access Through Your Firewall
Is your firewall or antivirus preventing legitimate network access? If you said, “What firewall?” or “What Antivirus?” stop reading this blog! You have far more pressing issues, primarily securing a new line of employment. If you are still reading, how do you handle network access issues? In my car, if you hit the button for Sirius XM radio, you will most likely find it tuned to 50’s music. I find it more appealing than today’s music, or at least the music of the last 30-40 years (results of a recent poll on MSN revealed I’m not alone). I often think I was born into the wrong era, however, if it were the 1950’s, I’d be in a whole different line of work, since IT as we know it did not exist. Security was much simpler then.
Today, we’re bombarded with wave after wave of constantly evolving IoT threats. The latest, Petya/NotPetya/Netya/Goldeneye hit last month. I wrote in a previous article about keeping your antivirus signatures up to date to secure your devices against threats such as WannaCry. If you’re one of those misguided souls that decided to go the route of putting a crime-fighting hero on retainer, you have a new option, after all, didn’t Pierce Brosnan already tackle Goldeneye as 007? Our IoT ecosystems, both in business and personally, are under attack from a great number of entry points. We walk a fine line between making our walls and barriers impenetrable while allowing legitimate traffic through. In a quote from Security Technologist Bruce Schneier, IoT
“is fundamentally changing how computers get incorporated into our lives.” “Through the sensors, we’re giving the Internet eyes and ears. Through the actuators, we’re giving the Internet hands and feet. Through the processing — mostly in the cloud — we’re giving the Internet a brain. Together, we’re creating the Internet that senses, thinks, and acts. This is the classic definition of a robot, and I contend that we’re building a world-sized robot without even realizing it.”
We had a recent incident with our home security system. Actually, I had a Tim, the Tool-Man Taylor moment. I’d sleepily stumbled to bed after watching a late ballgame and neglected to arm the security system. Sometime later, a noise in the house woke me, and I remembered I had not set the alarm. Now, if it were the 1950’s, my wife would grab a Louisville Slugger and coerce me to join her in traipsing through the house to lock down any unfortunate perimeter breaches.
No problem, I thought, I have the app on my phone right here by the bed. Still half-asleep, I punched in the keystrokes to arm the system. Suddenly, the alarm went off, jarring me fully awake. I grabbed my phone and turned to my wife, half-expecting to see her wielding the bat and pointing in the direction of the sound like Babe Ruth calling his shot. And I realized she was not in bed. She then appeared in the bedroom doorway wild-eyed, a la a surprised Jill Taylor, and I was sure I heard her shout, “Tim, what did you do?” Sheepishly, I said something about hitting the wrong button on the app. Then she turned and ran to the console, to punch in the code to silence the alarm, explaining to the agent monitoring the device that she was putting her husband on intruder alert.
Note here, that if you should attempt an intrusion stunt at my home as a result of this article, be sure to pick a night when my memory is in full function. The sound of the alarm will probably provide plenty of lead time to avoid personal injury. If you are unfortunate enough to pick the wrong night, on the rare occasion the alarm has not been activated, you might have more to fear than my wife’s Babe Ruth impersonation. The next sound you hear will be the racking of my 12 gauge as I chamber a round and point in your general direction. Bring fresh underwear, you have been forewarned! The point is ladies and gents, don’t leave your firewall or antivirus disarmed.
We have so many entry points now with connected devices, and we as a company are always trying to keep our clients aware of where vulnerabilities lie. On the subject of keeping your security activated, I recently assisted one of our smaller clients with an issue of network connectivity after I had deployed a new hardware firewall and Vipre Internet Security Pro for Small Office antivirus. Users could no longer scan from the scanner across the network to their PC’s. In addition, as this is a small office with no server on site, the accounting package is hosted on one PC and accessed across the network. Users also could not access the computer hosting the company files. After a tech support call to the vendor, where they questioned the settings on the firewall, I reviewed the configuration. Then, I was notified that file access had been restored, and I found that the scanning issue had also been resolved. Curious, I took a look at the host PC, and discovered the vendor’s support team had indeed restored communication, but at the sacrifice of Vipre’s firewall. It had been disabled. I also found I could now scan to this computer only. Looking into the Vipre AV application, I found that there is a Learning Mode feature in the firewall to make adding exceptions easier. I turned the firewall back on, opened the Vipre Internet Security Pro Small Office interface, and followed these steps to enable Learning Mode:
Steps to Enable Learning Mode on Vipre AV
- Click Manage tab > Firewall
- Scroll all the way down until you see Firewall Default Behaviors
- Change the settings to Learning Mode
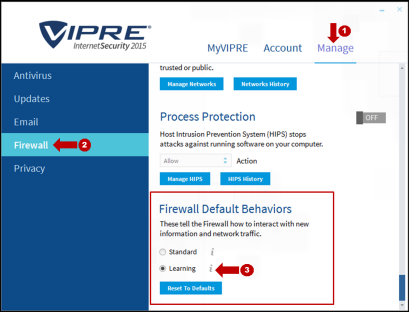
- Click Reset on the prompt that appears

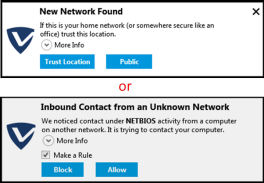
After that, the VIPRE Firewall is now in Learning Mode. You should try re-running the program that was having issues. If the Firewall was blocking the program, you will see one of the prompts (shown in the screenshots below) in the top right corner asking about an Inbound or Outbound Contact on your network. The name of the program will be in the information below. To allow the program, check the box for make a rule, and press allow.
Note: Keep in mind that there might be multiple prompts for multiple programs, so there may be a number of prompts that appear.
Once the above has been done and all subsequent pop-ups have passed, and you are confident all the allowances have been made and the firewall is properly configured, please reset the firewall to “Standard Mode”. Use the same procedure as above ensuring that the checkbox for “Delete all user defined rules” remains unchecked. After that, your Firewall will be back in Standard Mode and will run automatically with no prompts.
The importance of keeping your firewall and antivirus activated and updated cannot be overstated in today’s world. Ensure you have the proper tools to manage them. “Never give up, never surrender!” In a Star Trek parody, I remember from a few years ago, there is a device, Omega 13 that evil aliens want to get their hands on. The show revolves around characters of a cancelled TV show, Galaxy Quest. In the TV show, Omega 13 had been developed, but its purpose was not unveiled before the show was cancelled. A real race of aliens, the Thermians, recreated the Galaxy Quest spaceship including the Omega 13 device and brought the unsuspecting show characters onboard as the crew. No one knew what Omega 13 actually did; it could either destroy all matter in the universe or rewind time by 13 seconds, “enough time to undo a single mistake”. It turned out to be the latter we found out, as they deployed it late in the movie. What an intriguing concept Omega 13 would be as a tool to have in your arsenal, but you couldn’t count on using it if you’ve been compromised because you didn’t have proper security in place. For the record, you’d need way more than 13 seconds to get your firewall deployed, or to even update your antivirus signatures. Most likely, it might have been 13 minutes, 13 hours, 13 days, or more before you were even aware of the breach if you weren’t properly protected. Omega 13, however, would have enabled me to undo my single mistake of incorrectly arming my security system, and Babe Ruth would’ve been none the wiser. Shields up!
About The Author
Donny Hilbern is a network and systems consultant specializing in analyzing, designing, and implementing network and enterprise systems. Donny has been working in the IT field for over 25 years, with nearly 20 years of that time invested in network and system administration and infrastructure technology. He has experienced a number of undocumented or lightly documented issues during that time. His desire is to leverage that experience in sharing about some of those issues and how they were resolved to make IT work for his clients.
Need Firewall and Antivirus Help for Your Business? We’re on it!
Just think of the peace of mind and relief that will come from handing this off to our professional security and infrastructure team. Your team isn’t pulled away from their daily tasks and you avoid the frustration that comes with not being prepared. Start the conversation by completing the form below or give us a call at 405.810.8005.





Leave A Comment