We recently migrated a client from an SBS 2008 environment to a Server 2016 Hyper-V environment. As we waded through the migration, we found that the server had a number of issues in addition to several non-standard configurations implemented by a former MSP provider. I began to dismantle the services on the SBS server and discovered that, although I could open Server Manager, I could not access the Roles and Features utilities. Thus, began my tech version of the Circle of Frustration.
I needed to remove the CA role but couldn’t get to the utility to do it. Fine, I said, I removed Exchange via cmd line and the Exchange Management Shell, there must be a cmd line function for removing the CA role too. There is! And I’m sure it works great on Server 2012 and up, but those commands aren’t available in 2008, argh! So, researching further, to fix the Roles and Features function in Server Manager, I needed to install Windows Updates. Yeah, tried that too and Windows Updates was broken as well. I tried resolving that issue, but SBS wasn’t having it. One way of fixing that issue was to reinstall the server. Hah, fat chance! This server is going away, I’m not rebuilding it, only to turn around and decommission it. As the circle began closing in on me, a thought occurred – I’ll try managing the SBS server from Server Manager on a 2016 server. Brilliant, huh? Only, server versions 2012 and up can’t manage 2008-2008R2 servers without updating certain features on those older servers. OK, no problem, right? We’ll just do that. Only, none of the updates to accomplish my goal would install on the SBS server. At this point, my frustration level was nearly through the roof!
You can’t solve current problems with current thinking. Current problems are the result of current thinking.
Einstein said, “You can’t solve current problems with current thinking. Current problems are the result of current thinking.” That’s what was keeping me trapped inside the circle. Once I realized it, I could turn my attention to ways of escaping it. In Ground Hog Day, Bill Murray’s character, Phil Connors keeps repeating the same day over and over, caught in a frustrating circle. Phil, with all his character flaws, keeps trying different methods of breaking out of that circle. No matter what method he tries, he always finds himself starting the day over. Not until he changes his way of thinking and overcomes his flaws does he break the cycle. He learns contentment, forgiveness, and kindness.
Lost time is never found again.
Ben Franklin said, “Lost time is never found again.” I was never going to get that time back, but instead of continuing to try and fix a multitude of problems that may have not have even been realistically fixable, I changed my way of thinking. There is a much simpler way to resolve this and stop all the frustration. Just remove the server from the network, from Active Directory, heck, just totally remove it from existence! Then I can clean up the remnants from AD. Looking back now, that was even much easier done than said. Yep, you read that right. The bottom line was that the machine was going away – quit trying to fix it and just get rid of it already. I had let the analytical part of me control my progression towards reaching my goal. There is a point where you have to show the machine who’s boss. Enough time spent on this project. Time to take this sucker down!
I ran dcpromo to verify the demotion would not succeed under normal procedure, which, of course failed. And, I tried dcpromo with the /forceremoval option, which failed as well – just to cover all the bases. So, if you find yourself in a spot where you need to manually demote, remove and decommission your aging SBS server, here are the steps to accomplish the task:
Note: In my case I needed to manually remove the CA role before demoting the server. If you do not have this problem, you can skip to the section on Manually demoting, removing, and decommissioning the SBS server. (The CA role is installed automatically with SBS 2008, and 99% of the time, you can safely remove this role with no ill effects. As a precaution, I’m also including the steps to backup the CA in case it needs to be resurrected in the future on a new server.)
How to Backup the CA (as a precaution)
- Open an administrative cmd prompt.
- Type exe –backupdb C:\CABackup and press ENTER to backup the database.
- Typeexe –backupkey C:\CABackup and press ENTER to backup the certificate keys.
Note: You will be asked to enter a password to protect the keys.
- Type net stop certsvc and press ENTER to stop the Active Directory Certificate Services service.
- Type reg export HKLM\SYSTEM\CurrentControlSet\Services\CertSvc\Configuration C:\CABackup\CAregistry.reg and press ENTER to export the registry key to a file.
- You may also need to copy the CAPolicy.inf file from %SystemRoot% directory (if using custom policy). Verify your backup files are present at the location you specified and copy them to a safe location.
How To Manually Remove Certificate Authority (CA)
Do not delete any objects related to other PKI installations than the CA you are about to clean up!
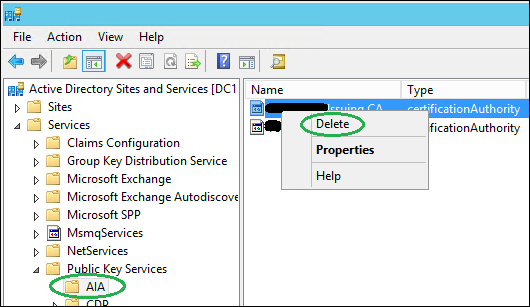
- Start Active Directory Sites and Services. (If you don’t see the Services node, make sure Show Services Node is checked).

- Expand Services/Public Key Services/AIA, right-click the object in the right pane matching your CA server and click Delete, select Yes to confirm.
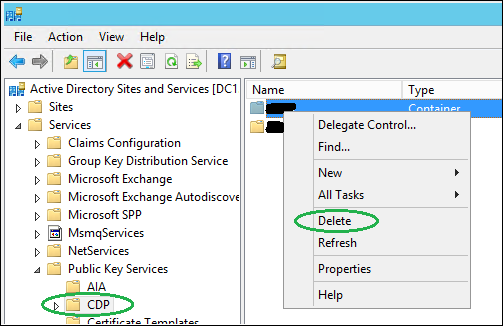
- Select the container CDP, right-click the container in the right pane matching your CA server and click Delete, select Yes twice to confirm.
- Select the container Certification Authorities. Make sure you aren’t removing information about a Subordinate CA as it likely your Root CA and could have other dependencies. If you’re removing information about an Enterprise Root CA you can proceed. Right-click the object in the right pane matching your CA server and click Delete, select Yes to confirm.

- Select the container KRA, right-click the object in the right pane matching your CA server and click Delete, select Yes to confirm.
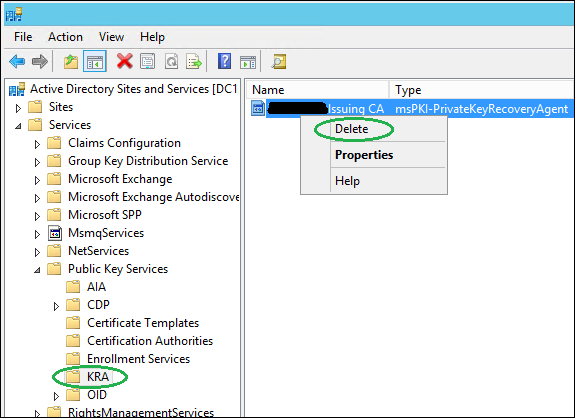
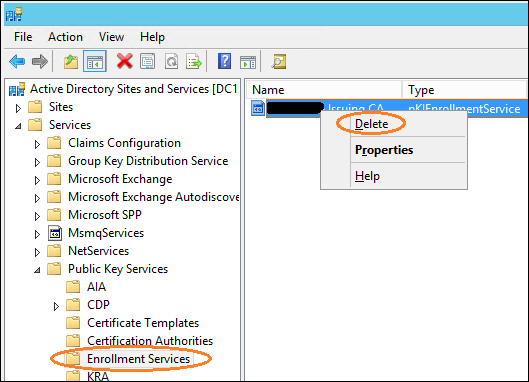
- Select the container Enrollment Services. You must also manually remove the pKIEnrollmentService object. Right-click the object in the right pane matching your CA server and click Delete, select Yes to confirm.
- Now we have to delete the CA-server from the NtAuthCertificates object, which is a little different, as it is a value in an existing AD object. Copy the following certutil command so you can paste it into Notepad and edit it, changing the highlighted Forest Root information to match your environment: certutil -viewdelstore “ldap:///CN=NtAuthCertificates,CN=Public Key Services,CN=Services, CN=Configuration,DC=contoso,DC=com?cACertificate?base?objectclass=certificationAuthority”
- At an administrative Powershell prompt (must be Enterprise Admin), run your edited certutil command. You’ll be prompted with a list of certificates in the NtAuthCertificates object.
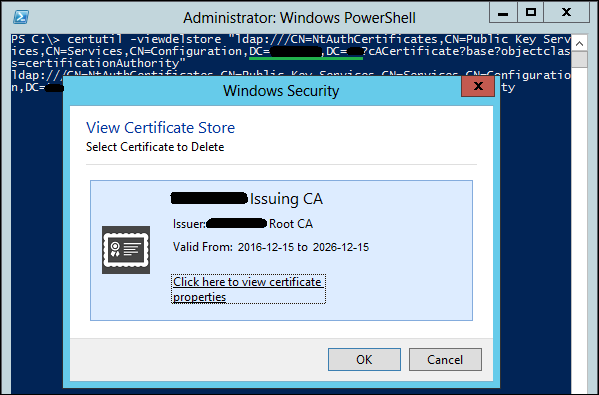
- Ensure you select the correct CA certificate as there could be more than just one, then click OK. If you choose Cancel you will abort any deletion attempts. The CA role has now been removed.
How To Manually Demote, Remove, and Decommission a SBS Server
1. If you have not yet transferred the FSMO roles to another DC, now would be the time to do that. It’s easier and much cleaner to transfer them than to seize them after the fact.
2. First, pull the plug, or shut down properly, and the network connection on the SBS server and never ever turn it back on while connected to the network.
3. To clean up the metadata using ntdsutil, open an administrative cmd prompt.
- Type “Ntdsutil”, and then press Enter.
- Type “metadata cleanup”, and then press Enter.
- Type “connections”, and then press Enter.
- Type “connect to server “, where is the name of the working DC you want to use to perform the cleanup, and then press Enter.
- Type “quit”, and then press Enter.
- Type “select operation target”, and then press Enter.
- Type “list domains”, and then press Enter.
- Type “select domain [n]”, [n] representing the domain, and then press Enter.
- Type “list sites”, and then press Enter.
- Type “select site [n]”, [n] representing the site, and then press Enter.
- Type “list servers in site”, and then press Enter.
- Type “select server [n]”, [n] representing the DC to be removed, and then press Enter.
- Type “quit”, and then press Enter.
- Type “remove selected server”, and then press Enter.
Note: At this point for me, the ntdsutil removal process failed because the old server could not be found. This was quite possibly due to the fact I had already removed the server from ADUC previous to performing the metadata cleanup.
4. Now, we’ll need to clean up any remnant metadata via Active Directory Users and Computers, so log in to your healthy DC server as Domain/Enterprise administrator and navigate to Server Manager > Tools > Active Directory Users and Computers.
5. Expand the Domain > Domain Controllers.
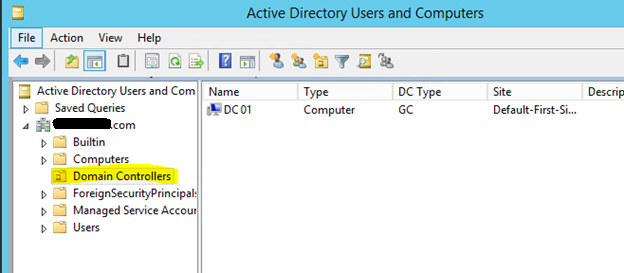
6. Right click on the DC server that you need to remove manually, if the object still exists, and click Delete.
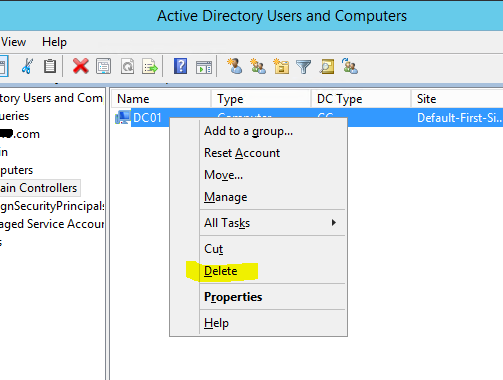
7. Click Yes to confirm.

8. Next, select Delete this Domain Controller anyway. It is permanently offline and can no longer be removed using the removal wizard and click Delete.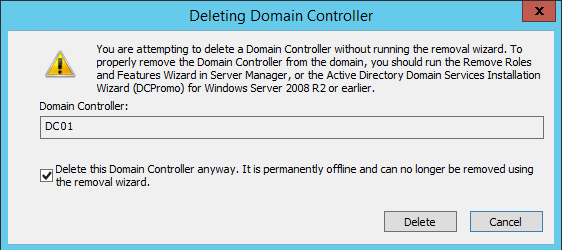
9. If the domain controller is a global catalog server, then in the next window click Yes to continue with the deletion.
10. If the domain controller holds any FSMO roles, then in next window, click ok to move them to a domain controller which is available. Idealistically, you should have already transferred those roles and checked your configuration previous to getting this late in the game.
11. To clean up the DC server instance from the Active Directory Sites and Services, go to Server Manager > Tools > Active Directory Sites and Services.
12. Expand the Sites and go to the server that needs to be removed if the object still exists, right-click and click Delete.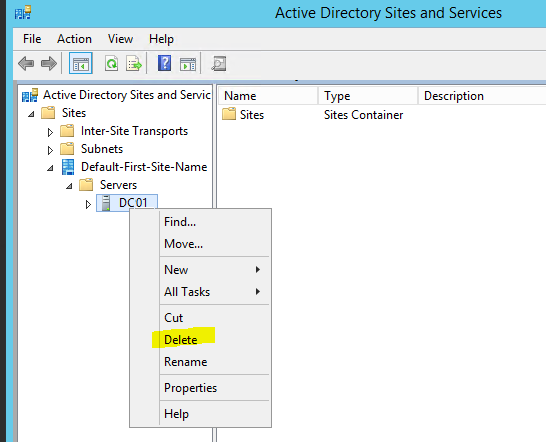
13. Click Yes to confirm.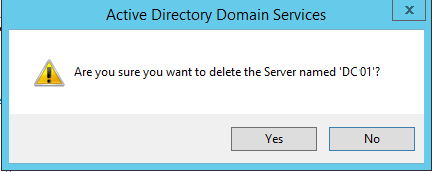
14. To cleanup DNS by removing all references to the removed server, in the DNS snap-in, right-click on the domain and select Properties.
15. Click on the Nameservers tab: remove the server.
16. Repeat the above instructions for Reverse lookup and all zones.
17. Open up _msdcs and check all folders within for the old server name or IP reference.
18. Repeat the above step for _sites, and all others.
19. Repeat the above steps for the Reverse lookup zones.
The process looks a lot more complicated than it actually is. However, it does perform some pretty dicey things in Active Directory, so for those who may be somewhat tech-challenged, you may defer the down and dirty details to your systems admin. You know, if you hear a term like cloud computing, and you’re thinking “computers can fly now?”, you might be a card-carrying member of that club. An SBS decommission can be stubborn, and when things just don’t go according to plan for various reasons, that server seems almost human. You feel disrespected, intimidated by the sound of maniacal laughing emanating from somewhere deep within that bucket of silicon and circuits. And in the midst of the laughter you’re pretty sure you heard it say “You want me to what?” Not really so far-fetched when you consider that there are reports of folks hearing Alexa arbitrarily burst out laughing. That’s when you need to implement the procedures outlined in this article to make the thing snap-to and say “Yes, sir”. If it’s a little too daunting for your comfort, partner with someone who’s been there before. We may not have slept at a Holiday Inn Express last night, but at our office, we know a thing or two because we’ve seen a thing or two … er something like that. Call or contact our staff, who can arrange a time to consult with you, and if necessary assist you in getting that obnoxious little SBS to sit up and pay attention. You need that circle of frustration to screech to a stop and your frustration level to wind back down into the green. After all, green is the important buzz word here. You don’t need server issues eating up your budget, you need to be about the business of making money. For that you need your IT systems to work for you, not against you and maybe you can gain back some of that time old Ben lost.
Server Migration & Network Support
Let our professional network team help with your server migration and infrastructure support needs. Start the conversation by completing the form below or give us a call at 405.810.8005.
About The Author
Donny Hilbern is a network and systems consultant specializing in analyzing, designing, and implementing network and enterprise systems. Donny has been working in the IT field for over 25 years, with nearly 20 years of that time invested in network and system administration and infrastructure technology. He has experienced a number of undocumented or lightly documented issues during that time. His desire is to leverage that experience in sharing about some of those issues and how they were resolved to make IT work for his clients.





Hey Donny, I recently found myself in this situation and your article was just what I was looking for. Thanks for writing it!
Yep, I was driving to work this morning still debating on whether I should waste time jumping through all the errors or just seize all the roles and cleanup DNS. Your steps are a more graceful way in the middle. Thanks.